Desentupimento de Caixa de Esgoto
Peça uma vistoria gratuita, visitaremos sua empresa ou residencial para verificar o problema.

Desentupimento de Ralo
Peça uma vistoria gratuita, visitaremos sua empresa ou residencial para verificar o problema.
Desentupidora Goldentec Preço Justo e Visita Grátis
Desentupidora Goldentec serviços de desentupimento e dedetização, ligue agora e solicite um orçamento sem compromisso.

Desentupidora de Vasos Sanitários Goldentec

Desentupidora de Pias Goldentec?

Desentupidora de Pias Goldentec?

Desentupidora de Calhas Goldentec

Desentupidora de Caixas de esgoto Goldentec
Desentupidora de Canos Goldentec
A grande maioria das desentupidoras de esgoto não possuem equipamentos adequados para resolver alguns tipos de entupimento em casas ou prédios e informam que é necessário quebrar pisos ou paredes do local da casa para resolver o problema.
Se isso estiver acontecendo com você, antes de tomar uma atitude sem pensar procure entrar em contato agora mesmo com a Goldentec, possuímos todos equipamento adequado e várias equipes de profissionais dedicados para lhe oferecer uma solução rápida e limpa, e capaz de retirar do caminho da tubulação a maioria dos diversos problemas de entupimento que estejam bloqueando a passagem da água limpa ou suja.
- DESENTUPIMENTO DE RALOS DE BANHEIRO E QUINTAL
- DESENTUPIMENTOS DE RAMAIS ESGOTOS EM GERAL
- DESENTUPIMENTO DE VASOS SANITÁRIOS E PRIVADAS
- DESENTUPIMENTO DE PIAS E TANQUES
- DESENTUPIMENTO DE CALHAS DE ÁGUAS PLUVIAIS
Qual o Tipo de Problema com entupimento?
- ATENDIMENTO EMERGENCIAL COM A DESENTUPIDORA GOLDENTEC.
- MÁQUINAS DE DESENTUPIR ESGOTO MODERNAS QUE NÃO DANIFICAM TUBULAÇÕES.
- ATENDIMENTO PONTUAL COM A HORA MARCADA.
- REALIZADO ORÇAMENTO PARA QUE SEJA FEITO O SERVIÇO.
- VÁRIAS FORMAS DE PAGAMENTO , CHEQUE, CARTÃO, DINHEIRO, DEPÓSITO E BOLETO (COM CONSULTA).
- QUALIDADE E GARANTIA PARA TODOS OS ATENDIMENTOS.
Entenda como é feito o serviço de desentupimento.
Ligue e agende uma visita com nossa equipe. Realizamos serviços de desentupimento em seu imóvel com uma vistoria para ser visto o que tem que ser feito, depois disso passamos o valor que vai ser cobrado e se aprovado o serviço de desentupimento é realizado na hora pelo mesmo técnico que está fazendo a visita.
Nós da Desentupidora Goldentec Fornecemos certificado por escrito em todos os nossos serviços de desentupimento, depois que o serviço é realizado o certificado é emitido com o tempo de garantia que é dado para o serviço resolvido, tendo em vista que para cada tipo de serviço e local o tempo de garantia muda.
VEJA OS VÍDEOS

Como é feita a solicitação da desentupidora para desentupir Goldentec?
- Ligue no Telefone da Goldentec desentupidora atendimento por telefone, chat, ou preencha ou mande pelo e-mail preenchendo o formulário.
- Peça uma vistoria gratuita, visitaremos sua empresa ou residencial para verificar o problema.
- Feito o orçamento gratuito, passaremos o orçamento mais barato do mercado.
- O Cliente Estando de acordo, será realizado o serviço no mesmo instante.
- Resolvido! Fim do Problema, o cliente ganha o cerificado de garantia do serviço.
Ligue e solicite uma vistoria gratuita.

Ligue e agende uma visita grátis.

Atendimento 24 Hs !!!
Oferecemos serviços profissionais de desentupidora Goldentec de:
Desentupimento de Vasos Sanitários: causado por obstruções como objetos rígidos, papeis higiênicos, escovas de dentes, fraudas, frascos de desodorantes etc, desentupimos vasos sanitários com maquinas desentupidora eletro rotativas erradicando o entupimento com a desentupidora Goldentec.
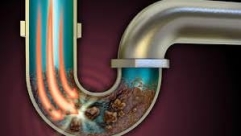
Desentupimento de Esgotos em geral: Quando se trata de desentupidora Goldentec 24h, os canos de esgotos são os que causam os maiores transtornos. Causado por diversos resíduos no interior dos canos, impede o fluxo natural do efluente. Oferecemos serviços completo de desentupidora de esgotos, eliminando as obstruções e fazendo uma raspagem interna da tubulação.
Desentupimento de Ralos: Para identificar o entupimento de ralo, observamos um empoçado de água que não escoa, causado por resíduos sólidos como fios de cabelos acumulados. Para solucionar este problema contamos com encanadores experientes com alto conhecimento técnico para atender esta necessidade.
Desentupimento de Pia: Ao usar a pia, a água não escoa, aumentando o volume de água dentro da cuba, provavelmente a pia esta entupida, a sua causa pode ser: restos de alimentos, gorduras ou fragmentos de resíduos sólidos. Oferecemos serviços de desentupidora de pia com profissionalismo, segurança e com toda garantia.
Desentupimento de Colunas: Atendemos Empresas em todas os Bairro de São Paulo. Realizamos um serviço de qualidade e eficaz, com elevada satisfação técnica, com várias formas de pagamento, 24 horas por dia, Segunda a Domingo e 50% mais em conta que muitas desentupidoras.
COMO RESOLVEMOS PROBLEMAS DE DESENTUPIR PIAS, RALOS, VASOS SANITÁRIOS.
Para resolver qualquer tipo de entupimento entre em contato agora mesmo que temos equipes disponíveis em seu bairro Goldentec para solucionar seu problema com qualquer tipo de entupimento, pode ser um ralo entupido como o esgoto completo da residência ou de uma fabrica, somos a melhor empresa de desentupimento do bairro de são paulo, porque além do atendimento imediato também oferecemos a nossos clientes o melhor custo pelo serviço de desentupimento.
Como é cobrado o Desentupimento de esgoto de residências e comércios?
Assim que Feito o Orçamento para desentupimento de esgoto de tubulações de pisos e paredes Goldentec e grande são paulo nossos técnicos irão realizar o desentupimento realizando a raspagem da tubulação com equipamentos de molas flexíveis que não danificam a tubulação até o ponto que está entupido.
Desentupidora Goldentec